Managing file permissions is a fundamental skill for any Linux user or administrator. Understanding how to recursively change the file’s permissions in Linux is crucial for system security and proper application functionality. This guide will walk you through the essential commands and best practices. We will cover everything from Basic permission concepts to advanced recursive techniques, ensuring your files and directories have the correct access levels.
Introduction to Recursive File Permission Changes in Linux
Linux file permissions dictate who can read, write, or execute files and directories. Incorrect permissions can lead to security vulnerabilities or prevent legitimate users and applications from functioning. Therefore, mastering permission management is a core aspect of Linux administration.
What are Linux File Permissions and Why They Matter?
Linux permissions control access to every file and directory on your system. They define what actions an owner, a group, or other users can perform. Properly set permissions prevent unauthorized access, data corruption, and system instability. They are a critical layer of security.
For instance, a web server needs specific permissions to serve files, but not to allow arbitrary writes. Similarly, sensitive configuration files should only be readable by the root user. Understanding these nuances helps maintain a secure and functional environment.
Why Recursive Permission Changes are Essential for Linux Systems
Imagine needing to adjust permissions for hundreds or thousands of files within a directory tree. Changing them one by one would be impractical and error-prone. This is where recursive permission changes become indispensable. They allow you to apply permission modifications to a parent directory and all its contents, including subdirectories and files, in a single command. This saves significant time and ensures consistency across a large number of items.
Understanding Linux File Permissions: The Fundamentals
Before you learn how to recursively change the file’s permissions in Linux, it is vital to grasp the basics. Linux permissions are divided into categories and types. This foundational knowledge will help you apply changes effectively and avoid common mistakes. Furthermore, it ensures you understand the impact of your commands.
Owner, Group, and Others: Defining Access
Every file and directory in Linux has three distinct permission categories. These categories determine who can perform actions on the item. Understanding each one is key to setting appropriate access controls.
- Owner (u): This is the user who created the file or directory. The owner typically has the most control.
- Group (g): This refers to a specific group of users. All members of this group share the same permissions for the file.
- Others (o): This category includes all other users on the system who are not the owner and not part of the assigned group.
Read, Write, Execute (rwx): The Core Permissions Explained
Within each category (owner, group, others), three types of permissions exist. These permissions define the specific actions allowed. They are fundamental to controlling access.
- Read (r): Allows viewing the contents of a file or listing the contents of a directory.
- Write (w): Permits modifying a file or creating/deleting files within a directory.
- Execute (x): Enables running a file as a program or accessing a directory (e.g., `cd` into it).
Symbolic vs. Octal Modes: Different Ways to Express Permissions
You can express permissions using two main modes. Both achieve the same result but offer different syntax. Understanding both helps you interpret and apply permission changes.
Symbolic Mode uses letters (u, g, o, a for all; r, w, x; +, -, =). For example, `u+rwx` adds read, write, and execute permissions for the owner. Octal Mode uses a three-digit number, where each digit represents the permissions for owner, group, and others respectively. Each permission (r, w, x) has a numerical value (read=4, write=2, execute=1). For instance, 755 means owner has rwx (4+2+1=7), group has rx (4+1=5), and others have rx (4+1=5).
The `chmod` Command Basics: Your Primary Tool to Change Permissions
The `chmod` command is your primary utility for modifying file and directory permissions in Linux. It allows you to specify permissions using either symbolic or octal modes. Learning its basic usage is the first step towards understanding how to recursively change the file’s permissions in Linux effectively.
Basic `chmod` Syntax and Usage Examples
The general syntax for `chmod` is `chmod [options] mode file(s)`. The `mode` specifies the permissions you want to set. You can apply this command to individual files or directories. For example, `chmod 644 myfile.txt` sets read/write for the owner and read-only for the group and others. This command is very powerful.
Applying Permissions with Symbolic Mode (e.g., `u+rwx`, `go-w`)
Symbolic mode is often more intuitive for incremental changes. You specify the category, an operator, and the permission type. Operators include `+` (add permission), `-` (remove permission), and `=` (set exact permission). For example, `chmod u+x myscript.sh` adds execute permission for the owner. Furthermore, `chmod go-w mydir` removes write permission for group and others from `mydir`.
Applying Permissions with Octal Mode (e.g., `755`, `644`)
Octal mode is concise and widely used for setting absolute permissions. Each digit represents the sum of read (4), write (2), and execute (1) for owner, group, and others respectively. Common octal values include `777` (full access for everyone), `755` (owner rwx, group rx, others rx), and `644` (owner rw, group r, others r). For example, `chmod 755 mydirectory` sets common permissions for a directory.
How to Recursively Change File Permissions in Linux with `chmod -R`
The `chmod -R` command is the cornerstone of recursive permission management. It allows you to apply permission changes to a directory and all its contents. This is incredibly useful for managing large project directories or web server files. It simplifies the process significantly.
Syntax and Practical Examples of `chmod -R`
The `-R` option stands for “recursive.” When you use it, `chmod` processes the specified directory and then traverses into all its subdirectories, applying the same permission changes to every file and directory it encounters. The syntax is `chmod -R [mode] [directory]`. For example, `chmod -R 755 /var/www/html` would set `755` permissions on the `html` directory and everything inside it.
Consider a scenario where you’ve uploaded new website files. You need to ensure they are all readable by the web server. You could use `chmod -R 644 /path/to/website`. This command makes all files readable by the owner, group, and others, while only the owner can write. This is a common and secure setting for web content. However, be cautious when using `chmod -R` with sensitive directories.
Applying Permissions Recursively to Both Files and Directories
When you use `chmod -R`, the specified mode applies uniformly to both files and directories. This can sometimes be problematic. For instance, directories typically need execute permission (`x`) to allow users to `cd` into them and list their contents, whereas files only need `x` if they are executable scripts or programs. A common practice is to set `755` for directories and `644` for files. We will explore how to achieve this granular control in the next section.
Common Mistakes When Using `chmod -R` and How to Avoid Them
Using `chmod -R` incorrectly can have serious consequences. A common mistake is applying overly permissive permissions, like `chmod -R 777`, which grants full read, write, and execute access to everyone. This creates significant security risks. Always use the least restrictive permissions necessary.
Another pitfall is running `chmod -R` from the wrong directory or with the wrong target path. Always double-check your current working directory (`pwd`) and the target path before executing a recursive command. Furthermore, consider testing on a small, non-critical subset first. Always understand the implications of the mode you are applying.
Advanced Recursive Permission Changes: Using `find` with `chmod`
While `chmod -R` is powerful, it applies the same permissions to both files and directories. Often, you need different permissions for each. This is where the `find` command, combined with `chmod`, becomes invaluable. It offers much greater control when you need to recursively change the file’s permissions in Linux.
Recursively Changing Permissions for Files Only (`-type f`)
To change permissions exclusively for files within a directory tree, you can use `find` with the `-type f` option. This command identifies all files and then executes `chmod` on each one. For example, to set all files to `644` (read/write for owner, read-only for group and others) in the current directory and its subdirectories, you would use:
find . -type f -exec chmod 644 {} ;Here, `.` specifies the current directory, `-type f` filters for files, and `-exec chmod 644 {} ;` runs `chmod 644` on each found file. This ensures that only files receive the specified permissions, leaving directory permissions untouched.
Recursively Changing Permissions for Directories Only (`-type d`)
Similarly, you can target only directories using `find` with the `-type d` option. This is essential for ensuring directories have the execute bit set, allowing users to traverse them. To set all directories to `755` (read/write/execute for owner, read/execute for group and others) in the current directory tree, you would use:
find . -type d -exec chmod 755 {} ;This command correctly applies the typical `755` permissions suitable for directories. It prevents issues where users cannot access subdirectories. This method provides precise control over directory access.
Combining `find` with `exec chmod` for Granular Control
Using `find` with `-exec chmod` offers the most granular control over recursive permission changes. You can combine these commands to apply different permissions to files and directories within the same operation. This is often the recommended approach for web servers or complex application deployments.
- First, set permissions for all directories: `find /path/to/dir -type d -exec chmod 755 {} ;`
- Second, set permissions for all files: `find /path/to/dir -type f -exec chmod 644 {} ;`
This two-step process ensures that directories have the necessary execute bit, while files maintain a more restrictive permission set. It is a robust method for managing permissions effectively. This approach is superior to a single `chmod -R` for many scenarios.
Best Practices, Security, and Troubleshooting Recursive Permissions
Applying recursive permissions requires careful consideration of security and potential issues. Following best practices helps prevent common problems. It also ensures your system remains secure and functional. Always prioritize security.
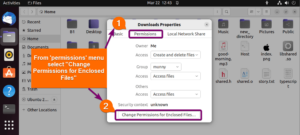
Securely Applying Recursive Permissions (e.g., Web Servers, Shared Environments)
When working with web servers or shared environments, security is paramount. Avoid `777` permissions at all costs. For web content, `755` for directories and `644` for files is a common and secure configuration. For scripts that need to be executed by the web server, `755` might be necessary. Always grant the minimum necessary permissions. Furthermore, consider using `chown -R` to set the correct ownership for files and directories, ensuring that the web server user (e.g., `www-data` or `apache`) is the owner or part of the group.
Common Pitfalls, ‘Permission Denied’ Errors, and How to Revert Changes
‘Permission denied’ errors are common when permissions are too restrictive. If you encounter these, first check the file’s owner, group, and permissions using `ls -l`. If you accidentally apply incorrect permissions, you might lose access to files. In such cases, if you have root access (via `sudo`), you can usually revert changes. For example, if you mistakenly ran `chmod -R 000 .`, you could use `sudo chmod -R 755 .` to restore access. Always have a backup or test on non-critical data. You can find more information about `chmod` on the Wikipedia chmod page.
Auditing and Maintaining Linux File Permissions Effectively
Regularly auditing your file permissions is a good security practice. Tools like `find` can help identify files with overly permissive settings. For example, `find . -perm 777` will list all files with `777` permissions. Implement a clear permission strategy for different types of files and directories. Document your permission settings, especially in complex environments. This proactive approach helps maintain system integrity and prevent security breaches. Therefore, consistent maintenance is crucial.
Frequently Asked Questions About Recursively Changing Permissions
Many users have common questions when learning how to recursively change the file’s permissions in Linux. This section addresses some of the most frequent inquiries. Understanding these answers will further solidify your knowledge and confidence.
What is the safest way to recursively change permissions?
The safest way involves using the `find` command combined with `chmod` to apply different permissions for files and directories separately. Typically, `find . -type d -exec chmod 755 {} ;` for directories and `find . -type f -exec chmod 644 {} ;` for files is recommended. This approach ensures directories have the necessary execute bit while files maintain more restrictive access, minimizing security risks.
Can I recursively change permissions for only specific file extensions?
Yes, you can use the `find` command with the `-name` option to target specific file extensions. For example, to change permissions for all `.php` files recursively to `640`, you would use: `find . -name “*.php” -type f -exec chmod 640 {} ;`. This provides highly specific control over your permission changes, which is very useful in web development contexts.
How do I ensure new files/directories inherit permissions automatically?
You can use the `umask` command to control the default permissions for newly created files and directories. `umask` specifies which permission bits are removed from the default. For instance, a `umask 022` results in new files getting `644` (666-022) and new directories getting `755` (777-022). You can set `umask` in your shell’s configuration file (e.g., `.bashrc`) to make it persistent.
What does `chmod -R go-w .` do and when should I use it?
The command `chmod -R go-w .` recursively removes write permissions for the group (`g`) and others (`o`) from all files and directories within the current directory (`.`). You should use this when you want to ensure that only the owner can modify files and directories, preventing accidental or malicious changes by other users or processes. This is particularly useful for configuration files or static website content.
Conclusion: Mastering Recursive File Permission Management in Linux
Learning how to recursively change the file’s permissions in Linux is a fundamental skill for any system administrator or power user. You now understand the core concepts of Linux permissions, the `chmod` command, and advanced techniques using `find`. Implementing these practices correctly enhances system security and ensures operational efficiency.
Key Takeaways for Secure and Efficient Permission Handling
Always remember to apply the principle of least privilege: grant only the necessary permissions. Use `chmod -R` with caution, and prefer `find -exec chmod` for granular control over files and directories. Regularly review your permission settings to maintain a robust and secure Linux environment. This proactive approach will save you from many potential headaches.
Continue Your Linux Journey: Further Resources and Best Practices
Continue to explore the vast capabilities of Linux commands. Practice these permission management techniques in a safe, non-production environment. Experiment with different `chmod` modes and `find` options. Your journey to mastering Linux administration is ongoing, and understanding permissions is a significant step. Share your experiences and questions in the comments below!
